Towage vessels and their crews are increasingly connected to online services during operations, increasing their vulnerability to cyber threats, malware, viruses and hackers.
These concerns were raised by the Maritime Transportation System (MTS) – Information Sharing and Analysis Center (ISAC) in the US after a tug was the victim of a phishing email.
This was the first time a tug reported receiving this type of phishing email, according to MTS-ISAC, which advised the whole maritime industry of the dangers of cyber attacks during Riviera Maritime Media’s Where port security meets cyber security webinar in August.
Its cyber security advisory said a tug operating organisation received the phishing email with a voicemail-themed attachment, then notified Louisiana InfraGard of the cyber threat, which notified MTS-ISAC.
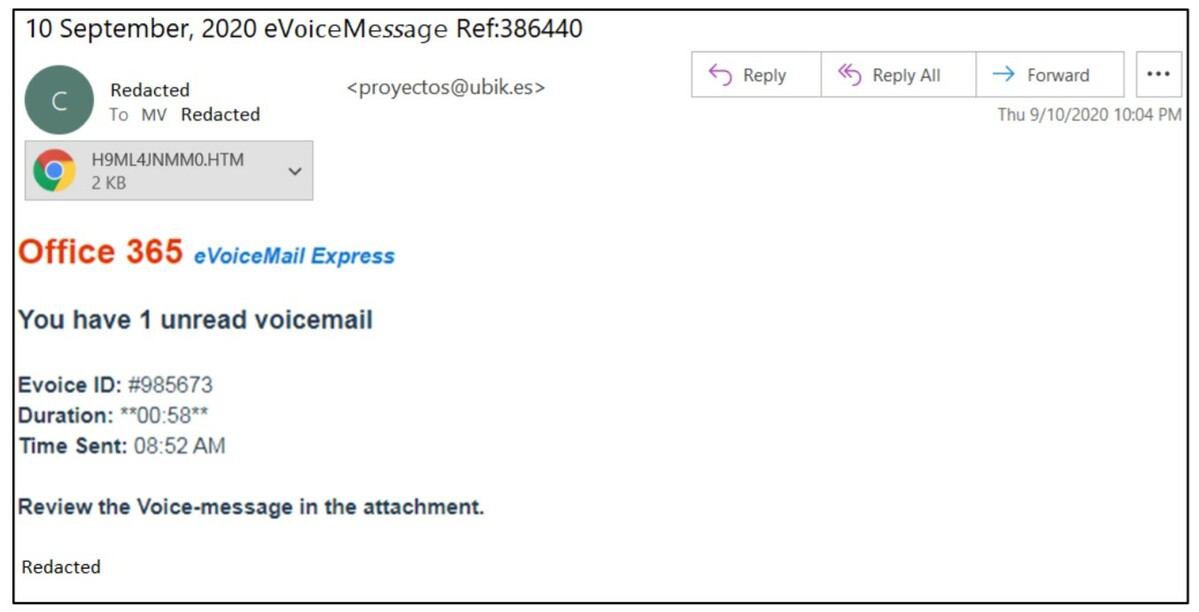
This malware email spoofed the vessel operator as the sender and was sent to the tug with an Office 365 eVoiceMail Express-themed attachment.
MTS-ISAC analysed the offending email, headers and the attachment. It discovered one of the HTTP (hypertext transfer protocol) requests received a 404 (not found) message and the other was not flagged as malicious when examined.
However, besides spoofing the vessel operator as the sender, the MTS-ISAC noticed that the email subject line used three different fonts, which may be an indicator that similar emails were sent to other prospective victims by replacing parts of the subject line text.
The sending IP address, which was geolocating to Germany, was associated with spam and phishing by multiple open source intelligence reports since June.
MTS-ISAC has asked other organisation to contact them if they receive similar activity through this link www.mtsisac.org/contact
It hopes its advisory increases tug operators’ situational knowledge and heightens their awareness of these cyber threats to their vessels and people.
MTS-ISAC explained some of the best practices to counter malicious email attacks in its advisory. Tug operators should provide regular email awareness training to employees, including how to handle links and attachments in emails, and help them understand how to identify and report suspicious emails to a security team.
Owners of towage vessels may need to implement additional email security technologies and tools to detect and filter spam and phishing attacks. Report suspicious activity for further analysis, trending and reporting to the maritime community, through the MTS-ISAC.
During Riviera’s Maritime Cyber Security Webinar Week in August, MTS-ISAC executive director Scott Dickerson explained how ports and ship operators can secure their assets from cyber threats.
He advised maritime organisations to be vigilant to the cyber threats to their assets. “Every organisation should understand their IT, operational technology and the risks to revenue generation and business models,” said Mr Dickerson, “and manage each risk to within the defined acceptable limits of the organisation.”