Cybersecurity has a huge potential to affect the safety of the crew, vessel, cargo and even ports. Cybersecurity is concerned with the protection of IT systems, onboard hardware and sensors and data leak from unauthorised access, manipulation and disruption. Cybersecurity policies and plans cover different types of risks like information integrity, system and hardware availability on board and in the office of the shipping company. Different incidents can be as the result of:
- Problems with data transfer from the shipping company to the vessel and vice versa. For example, incorrect transfer of charts from the shipping company to vessel’s ECDIS can cause delay in voyage or even possibility to reset all charts already installed on ECDIS
- Problems with onboard equipment and hardware. Not every member of the crew knows what to do with every operational equipment installed on board in case of disruption or even disaster. That can lead to more heavy consequences with vessel operations
- Loss of or manipulation of external sensor data, critical for the operation of a ship. Not to tell about the problems that may occur if vessel systems or shipping company systems will be attacked by hackers.
These are just examples of what can happen with the systems of the ship and the shipping company. With the development of information technologies in maritime logistics, such problems will arise more often if measures are not taken to prevent them in advance.
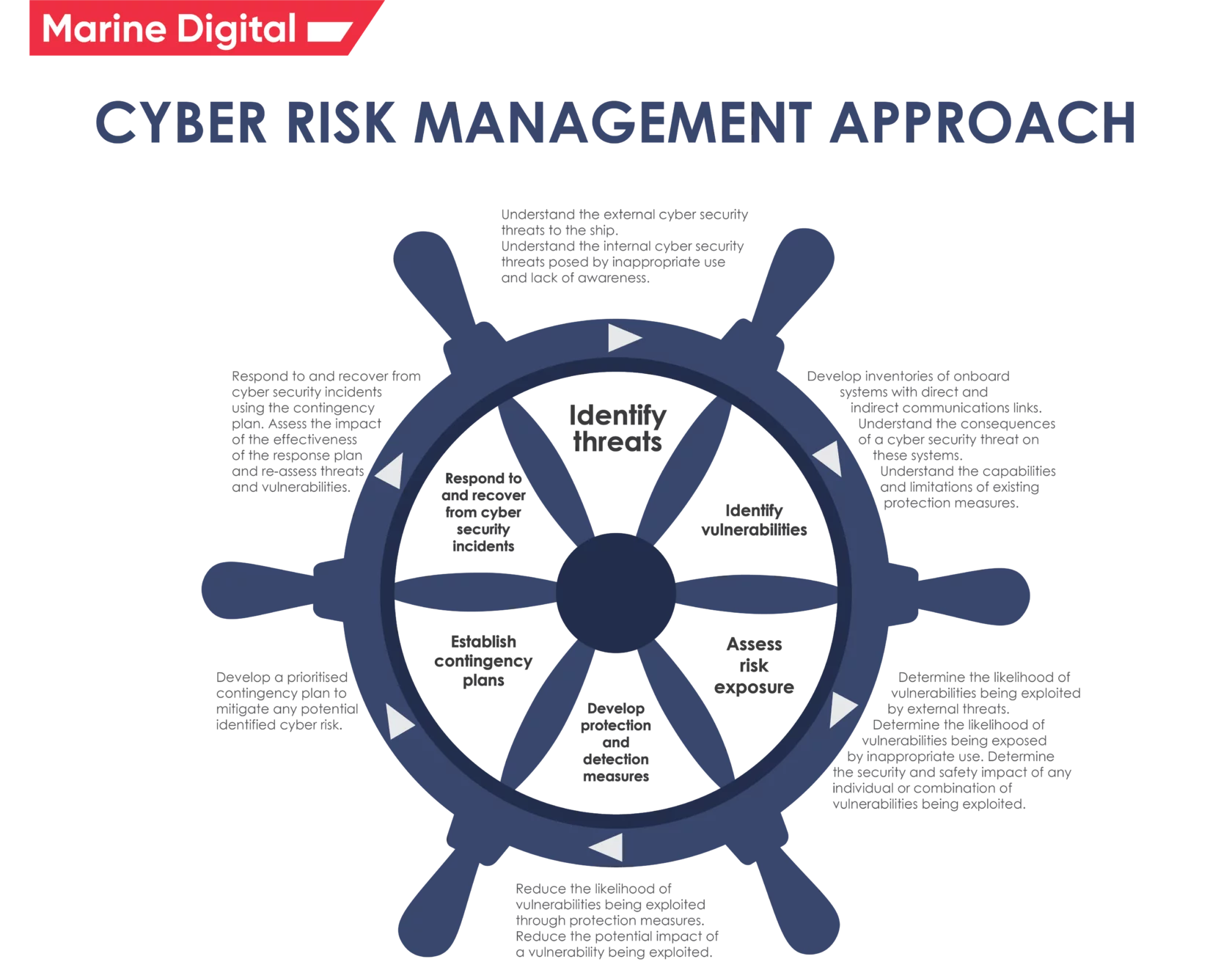
Cyber Risk Management should:
- Define the roles and responsibilities of users, key personnel and management both ashore and aboard
- Identify systems, assets, data and capabilities that, if breached, could pose a threat to the operations and safety of the ship
- Implement technical and procedural measures to protect against cyber incidents and ensure business continuity
- Carry out activities to prepare for and respond to cyber incidents.
The company’s Cyber Risk Management plans and procedures should complement the existing security risk management requirements of the ISM Code and the ISPS Code. Cybersecurity should be seen at all levels of the company, from top management onshore to onboard personnel, as an integral part of the safety culture required for the safe and efficient operation of a ship.
Vessels are increasingly integrated with onshore operations as digital communications are used to conduct business, manage operations, and keep in touch with office managers. In addition, critical vessel systems required for the safety of navigation, power supply and cargo management are increasingly digitized and connected to the Internet to perform a wide range of legitimate functions, such as:
- Monitoring of engine operation
- Service and management of spare parts
- Loading, handling, crane, pump control and laying planning
- vessel performance monitoring.
It is important to protect critical systems and data with multiple layers of safeguards that address the role of people, procedures, and technology to:
- Increase the likelihood of detecting a cyber incident
- Increase the effort and resources required to protect information, data or the availability of IT hardware.
Connected hardware on board should require more than one technical and / or procedural protection. Perimeter defenses such as firewalls are important to prevent unwanted intrusion into systems, but may not be sufficient to combat internal threats.
This defense in depth approach encourages a combination of:
- Physical safety of the vessel in accordance with the ship security plan (SSP)
- Network protection, including efficient segmentation
- Intrusion detection
- Periodic scanning and testing of vulnerabilities
- Software whitelist
- Access and user controls
- Appropriate procedures regarding the use of removable media and password policies
- Staff awareness of the risks and familiarity with the relevant procedures.
But how important is cybersecurity in the maritime industry?
Marine Digital Fuel Optimization System is a cloud-based system hosted at Amazon facilities in compliance with cybersecurity requirements.
AWS IoT Core provides automated configuration and authentication upon a device’s first connection to AWS IoT Core, as well as end-to-end encryption throughout all points of connection so that data is never exchanged between devices and AWS IoT Core without a proven identity.
AWS IoT Device Defender audits device-related resources (such as X.509 certificates, IoT policies, and Client IDs) against AWS IoT security best practices (e.g., the principle of least privilege or unique identity per device), continuously monitors our device fleets to detect any abnormal device behavior that may be indicative of a compromise by continuously monitoring high-value security metrics from the device and AWS IoT Core (e.g., the number of listening TCP ports on your devices or authorization failure counts).
Case study of data protection and cyber security by Marine Digital
Cyber risk management approach in shipping
Marine Digital FOS box (hardware part, which installed on a vessel) consists of a Data Collection Unit (DCU), a power supply, and a GSM modem, all-in-one robust enclosure, interfacing with the sources of input signals via a read-only NMEA connection, that pulls in data integrated sources, encodes and records it to the integrated storage, and then uploads the collected data to the cloud data lake when a GSM connection is available, autonomously from the shipboard systems. So there is no way to access the equipment on board.
Source: marine-digital
