America’s ports move approximately $5.4 trillion in goods annually, making them a unique target for cybercriminals. Protecting these transportation hubs is essential to preserving the supply chain and keeping the U.S. economy running.
More than 500 cyberattacks occurred in the marine industry in 2020, according to the U.S. Coast Guard. These exploits are aimed at both traditional port information technology systems and operational technology (OT) systems, which include the cranes, gantries, lifts and conveyance systems that move freight on and off ships.
The Coast Guard is the lead federal agency directly responsible for protecting America’s maritime transportation system. Its 2021 Cyber Strategic Outlook lays out specific responsibilities: “The U.S. Coast Guard will employ frameworks, standards and best practices in prevention and response activities to identify and manage cyber risks to the MTS. Within ports, the U.S. Coast Guard’s Captains of the Port will lead governance by promoting cyber risk management, accountability, and the development and implementation of unified response plans.”
The Coast Guard works directly with state and local governments in support of these duties, and more specifically with port authorities, which ultimately hold responsibility for the cybersecurity defenses of their regional seaports.
What Cybersecurity Vulnerabilities Do Maritime Facilities Face?
Seaports face familiar types of electronic assault: scanning, ransomware, malware, spear phishing and credential harvesting. In 2017, the shipping giant Maersk was laid low by the NotPetya worm, which scrambled the company’s IT and communications systems for two weeks, marking the largest maritime cybersecurity incident in recent years. That affected 76 ports across the globe, including the Port of Los Angeles, and 800 ships. In the end, the hack cost the company $300 million.
However, the Maersk attack was hardly the first. In 2011, the Belgian Port of Antwerp Bruges got hit by drug cartel hackers who surreptitiously took over the tracking of containers carrying hidden cocaine and heroin. The intruders accessed secure data giving them the location and security details of the steel boxes. That allowed the cartel to direct truck drivers to snatch them up before the legitimate owners of the cargo arrived. Port operators only got wise to the situation when they noticed containers inexplicably disappearing.
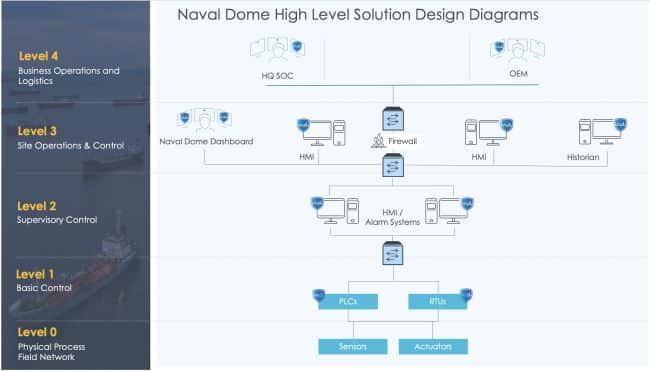
Seaports are complex facilities. While there is ample awareness of traditional IT vulnerabilities to networks, data and proprietary information, protection on the operational side is far behind, say experts. That includes cranes and container management systems, fuel terminals, shipboard controls, navigation systems, buoys, HVAC controls and more. Many are often creaky machines that have ancient, rudimentary electronic control systems.
“Operational technology is the most valuable thing in the network, and lives can be lost” without good oversight, says Rick Tiene, vice president with Mission Secure, Inc. The challenge is that the programmable logic control (PLC) boxes on maritime machinery are like 20-year-old computers, he says. “It’s a device that has an IP in/out and amps in/out.”
It’s so basic that cybersecurity technology can’t be added to it. Instead, Tiene’s company puts a protection envelope around PLCs.
“We put protection above it and below it,” he says. Practically speaking, that means monitoring the boxes for unusual power spikes that could indicate a cyber intruder has gained control.
How Do Ports Establish Maritime Cybersecurity Initiatives?
“OT is where you have higher risk exposure,” says Ian Bramson, global head of industrial cybersecurity for ABS Group. He adds that OT networks tend to be rickety and layered for years, and they require careful monitoring.
Ransomware may cost money, but monkeying with the valves of a fuel depot or the controls of a crane could be catastrophic. Ships are no less vulnerable. The scariest scenario is the cyber takeover of the ballast control system in a large ship, causing it to capsize and sink. While that hasn’t happened yet, Coast Guard and academic hackers have proven it’s possible, and Iran reportedly included the exploit in plans to disrupt fuel shipments.
The first thing a port needs to do to secure its OT system is to do an asset inventory, Bramson says. Then, a vulnerability assessment is needed to find holes. Next comes monitoring to see whether anyone else is already in the network. Is there any visibility in this area? “You have to get a vendor that knows OT,” he says.
ABS Group is technology-agnostic, but Bramson recommends such companies as Tenable and Claroty Cyber Assurance. There’s also the National Institute of Standards and Technology’s Cybersecurity Framework which is used by many companies to assess risk. It focuses on five areas: protect, detect, identify, respond and recover.
Tiene warns that paper assessments are not enough. Checking boxes to satisfy the top brass or standards organizations doesn’t equate to tangible cybersecurity.
“If that will get you a pass, they do the least they have to do,” he says. The margins in the maritime industry are thin. “Companies are reluctant to spend money on cybersecurity if the competition doesn’t have to.”
What Are Elements of a Strong Maritime Cybersecurity Initiative?
The Port of San Diego has dedicated cybersecurity staff to monitor, track and respond to threats, says Billy Marsh, the port’s CISO. “We treat our OT systems with the same rigor as our IT systems, and then focus on the individual risk assessment of each system to provide additional layers of security.”
Marsh says it’s best to audit thoroughly and frequently. The port uses next-generation firewalls, advanced endpoint protection and ingress filtering, among other technologies.
“A key strategy for security is to try and make it as transparent to the user as possible. If it’s a pain point in the workflow, people will sometimes try to find ways around it,” Marsh says.
He also recommends a patching schedule that covers operating system updates as well as software updates, multifactor authentication, and an incident response and disaster recovery plan for when something inevitably occurs.
In January, the Port of Los Angeles opened the Cyber Resilience Center, created to improve readiness and enhance its threat-sharing and recovery capabilities among supply chain stakeholders. The group currently includes 20 unnamed partners, including cargo handlers, terminal operators, shipping lines, and trucking and rail companies.
The central challenge was making sure the partners can communicate from different platforms, says Kevin Albano, associate partner at IBM Security X-Force, which built the system. “They needed a central place where information could be understood, and it was a priority to focus in on shipping containers.”
In 2020, stakeholders at the Port of New York and New Jersey formed a similar maritime cybersecurity coalition to improve information sharing among port users. The group includes the Coast Guard and the Area Maritime Security Committee, vessel operators, marine terminal operators, and representatives of the energy and financial sectors.
Soure:https://statetechmagazine.com/article/2022/07/how-americas-ports-defend-against-cyberthreats